Configure HTTP Basic Authentication with Control Center (Legacy) on Confluent Platform
HTTP Basic authentication is a simple way to implement access control. You can configure Confluent Control Center (Legacy) UI access control using HTTP Basic authentication. This authenticates users’ access to Control Center (Legacy).
You can also configure Control Center client authentication to other Confluent Platform components with HTTP Basic authentication enabled.
Note
For more sophisticated access control, Configure Role-based Access Control for Control Center.
Enable Basic authentication for Control Center (Legacy)
You can require a user to log in to Control Center (Legacy) by configuring HTTP Basic authentication using Java Authentication and Authorization Service (JAAS). JAAS provides a pluggable model, with details specified at runtime. For details on all configuration options, see UI authentication settings.
To configure Control Center (Legacy) authentication:
Specify the following options in the appropriate Control Center property file. Use the
confluent.controlcenter.rest.authentication.rolesandconfluent.controlcenter.auth.restricted.rolesto create groups of users; either administrators, which have full read and write access, or restricted users that have only read access. Restricted users cannot add or delete topics.Specify values for
confluent.controlcenter.rest.authentication.rolesin the following format:<administrator_group_name>,<restricted_group_name>The restricted value is the name of your restricted group:
confluent.controlcenter.auth.restricted.rolesis<restricted_group_name>.confluent.controlcenter.rest.authentication.method=BASIC confluent.controlcenter.rest.authentication.realm=c3 confluent.controlcenter.rest.authentication.roles=Administrators,Restricted confluent.controlcenter.auth.restricted.roles=Restricted confluent.controlcenter.auth.session.expiration.ms=600000
Create a JAAS file (
propertyfile.jaas) similar to the following. In the file, you specify the authentication realm as Control Center (Legacy) (c3), and provide the name of password file that will contain the Control Center (Legacy) users and passwords.c3 { org.eclipse.jetty.jaas.spi.PropertyFileLoginModule required file="/path/to/password.properties"; };
Your password file in
password.propertiesshould look similar to the following, specifying a username followed by a password and that user’s group, either the administrative group or the restricted group.Note
A user with membership in multiple groups is granted only the most restrictive permissions. For example, if a user is a member of two groups,
adminandreadonly, andreadonlyis a restricted role, then the user is granted only the rights for thereadonlygroup.admin: <admin-password>,<administrator_group_name> bob: <bob-password>,<administrator_group_name> alice: <alice-password>,<your_restricted_group>
Start Control Center (Legacy) passing in an argument to use the JAAS configuration, and specify the properties file that contains the HTTP Basic authentication settings:
CONTROL_CENTER_OPTS="-Djava.security.auth.login.config=/path/to/propertyfile.jaas" \ control-center-start ./etc/confluent-control-center/control-center.properties
When a user accesses Control Center (Legacy), they are shown a dialog similar to the one that follows, which prompts them for sign-in credentials.
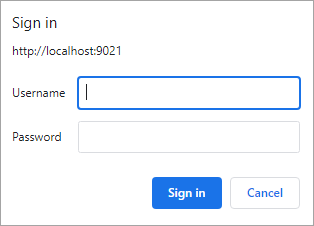
For this example, logging in as bob:<bob_password> provides read and write access. Logging in as alice:<alice_password> provides read-only access.
Restricted users
For users with restricted (read-only) roles, the following user interface (UI) features and options are unavailable/hidden:
Upload Connect configs
Browse connectors
Add, delete, pause, or resume connectors
View connectors settings
Create, delete, or edit alerts (triggers or actions)
Edit licenses
Edit brokers
Press submit on cluster forms
Edit, create, or delete schemas
Type in the ksqlDB editor
Add ksqlDB streams or tables
Control Center (Legacy) and other components
When HTTP Basic authentication is enabled on other Confluent Platform components, you must configure Control Center (Legacy) with a valid username and password for that component.
Basic authentication is enabled for Schema Registry
Whenever you have HTTP Basic authentication configured for Schema Registry, you must provide a username and password for Control Center (Legacy) to communicate correctly with Schema Registry. For a single cluster or the first cluster in a multi-cluster deployment, set the following properties, where the user.info contains a <username>:<password> that you have configured for Schema Registry.
confluent.controlcenter.schema.registry.basic.auth.credentials.source=USER_INFO
confluent.controlcenter.schema.registry.basic.auth.user.info=<sr-username>:<sr-password>
For multi-cluster deployment, to set the remaining clusters, use:
confluent.controlcenter.schema.registry.<sr-cluster-name>.basic.auth.credentials.source=USER_INFO
onfluent.controlcenter.schema.registry.<sr-cluster-name>.basic.auth.user.info=<sr-username>:<sr-password>
A multi-cluster deployment Schema Registry might look like the following:
// first Schema Registry cluster
confluent.controlcenter.schema.registry.url=<sr1-endpoint>
confluent.controlcenter.schema.registry.basic.auth.credentials.source=USER_INFO
confluent.controlcenter.schema.registry.basic.auth.user.info=<sr1-username>:<sr1-password>
// additional Schema Registry clusters
confluent.controlcenter.schema.registry.<sr2-name>.url=<sr2-endpoint>
confluent.controlcenter.schema.registry.<sr2-name>.basic.auth.credentials.source=USER_INFO
confluent.controlcenter.schema.registry.<sr2-name>.basic.auth.user.info=<sr2-username>:<sr2-password>
See Schema Registry for steps to configure HTTP Basic authentication for Schema Registry.
Basic Authentication for REST Proxy
To learn about using HTTP Basic authentication with REST Proxy, see HTTP Basic Authentication.
Basic Authentication is enabled for Connect
Whenever you have HTTP Basic authentication configured for Connect, you must provide a username and password for Control Center (Legacy) to communicate correctly with Connect. Set the confluent.controlcenter.connect.<connect-cluster-name>.basic.auth.user.info property to a value that contains <username>:<password> that you have configured for Connect.
confluent.controlcenter.connect.<connect1-name>.basic.auth.user.info=<connect-username>:<connect-password>
See Connect REST API for steps to configure HTTP Basic authentication for Connect.
Basic authentication is enabled for ksqlDB
Whenever you have HTTP Basic authentication configured for ksqlDB, you must provide a username and password for Control Center (Legacy) to communicate correctly with ksqlDB. Set the confluent.controlcenter.ksql.<ksql-cluster-name>.basic.auth.user.info property to a value that contains <username>:<password> that you have configured for ksqlDB.
confluent.controlcenter.ksql.ksql-cluster-name.basic.auth.user.info=<ksqal-username>:<ksql-password>
See ksqlDB for steps to configure HTTP Basic authentication for ksqlDB.