Important
You are viewing documentation for an older version of Confluent Platform. For the latest, click here.
Manage RBAC roles with Control Center¶
Manage RBAC role assignments (role bindings) for users and groups to a cluster scope and resource scopes in the Control Center UI. You can add and delete role assignments. Role assignments cannot be edited; you must delete an assignment and add it again for any necessary changes. Role assignments in Confluent Platform RBAC operate on an allow model only. Deny role assignments are not supported. Only predefined (built-in) roles are supported; custom roles are not supported.
Prerequisites¶
- RBAC is enabled for Control Center and all Confluent Platform components in your environment. Refer to the Prerequisites in the Control Center RBAC configuration documentation.
- You are assigned an appropriate role to manage RBAC role assignments in Control Center.
Role permissions required for managing roles¶
If you have the appropriate role permissions, you can administer RBAC role assignments in the Control Center UI rather than using the Confluent CLI. The following predefined RBAC roles can manage roles or view roles for other users in Confluent Platform:
SystemAdminUserAdminResourceOwner(for their respective resources only)SecurityAdmin(can view but not manage other user roles)Note
The
SecurityAdminrole has permission to view the Cluster roles and Resource roles, but does not have permission to add or remove roles. The add and remove roles buttons are not visible to those with only aSecurityAdminrole.
Important
If a principal is a Kafka super.user but does not have a role
assignment, they cannot view or assign roles using the Control Center
UI. The super.user can still use the CLI to assign roles. For
more information on super.user access and use, see
Troubleshoot role assignments.
For complete descriptions of each role, review the Roles page in the UI and the RBAC predefined-roles documentation.
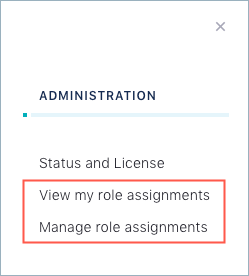
When RBAC is enabled for Control Center, and you have the proper role permissions, the View my role assignments and the Manage role assignments options appear on the Control Center Administration menu:
If you do not have a role that allows managing RBAC role assignments, the Manage role assignments option does not appear in the Administration menu.
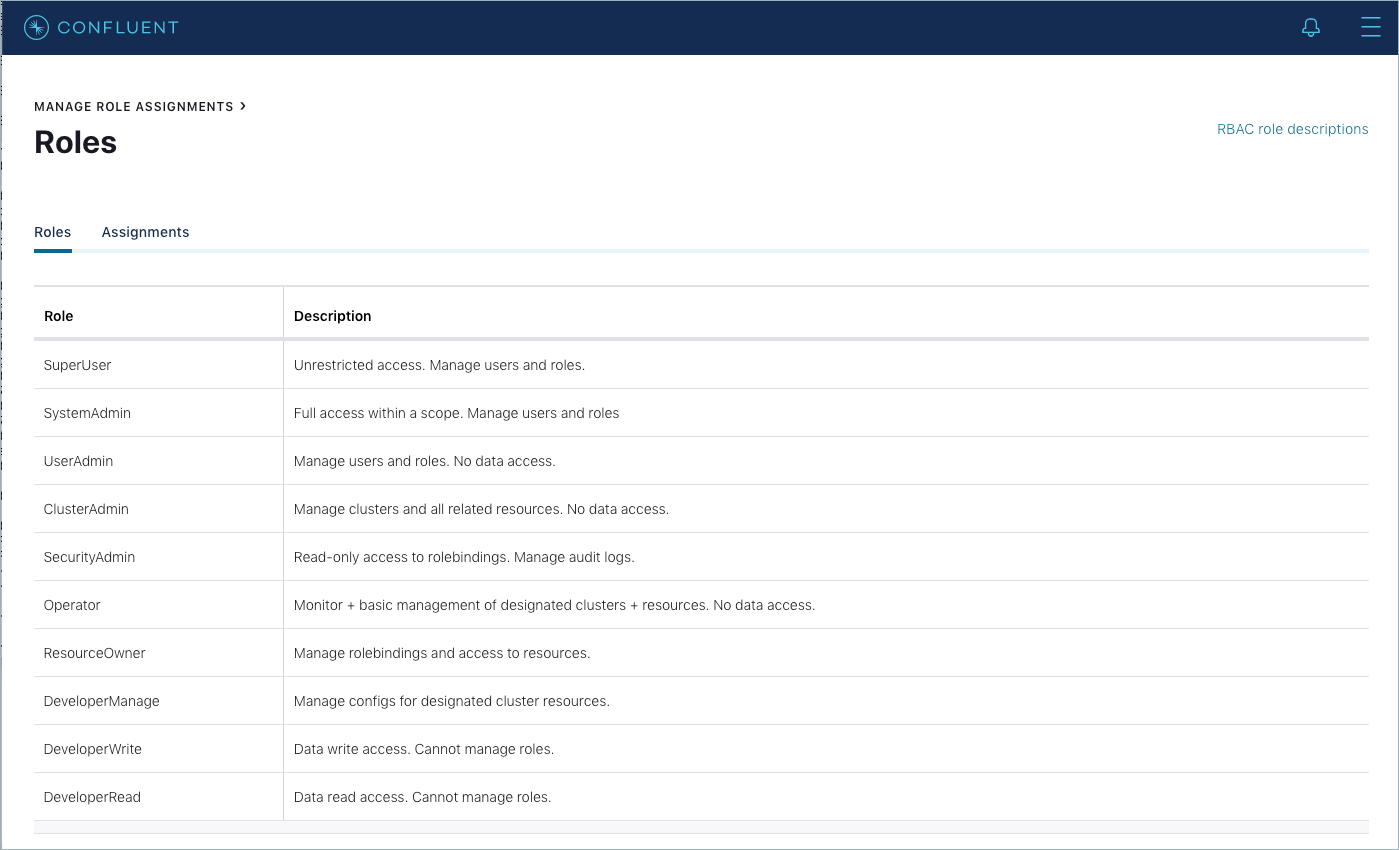
Roles page¶
To access the Roles page, click the Manage role assignments option from the Control Center Administration menu.
Use this page to view the available RBAC roles and their descriptions.
Note
There are no actions to take on this page; it is for informational purposes only.
Tip
Click the RBAC role descriptions link to access the RBAC predefined-roles documentation.
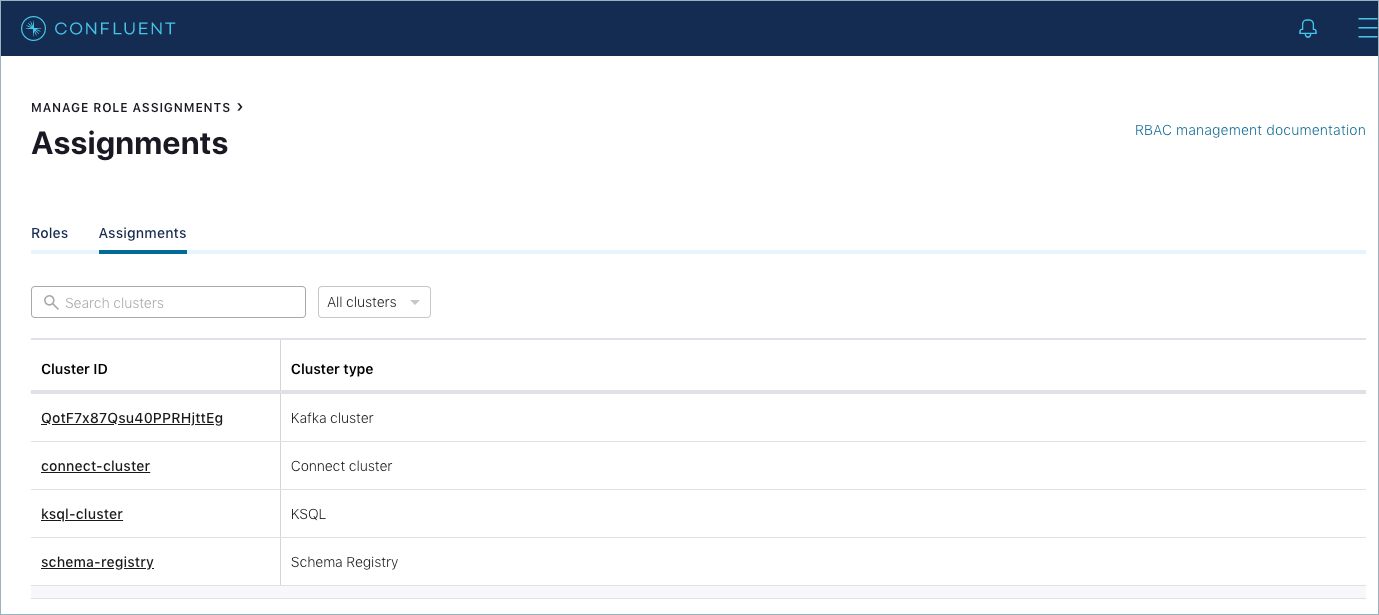
Manage Role Assignments page¶
To access the Assignments page:
- From the Control Center Administration menu, click the Manage role assignments option.
- Click the Assignments tab.
Use this page to:
View the clusters for which you can manage permissions.
Search for clusters by name and ID.
View existing cluster-level assignments.
Filter the cluster view by cluster type: Connect, Kafka, ksqlDB, Schema Registry.
Note
If there is only one type of cluster for which you are authorized to manage role assignments, the Cluster type (All clusters) list does not appear. Only the cluster types that you have role permissions to manage appear in the list.
Drill into a cluster to access the Cluster roles and Resource roles pages where you can add and delete role assignments for Groups and Users.
Add a role assignment¶
Add a role assignment (role binding) using the Control Center UI. You must have an appropriate role to add a role assignment.
To use the CLI to add a role assignment, see confluent iam rolebinding create.
You can add up to a limit of 1,000 role bindings. For more information, see RBAC limitations.
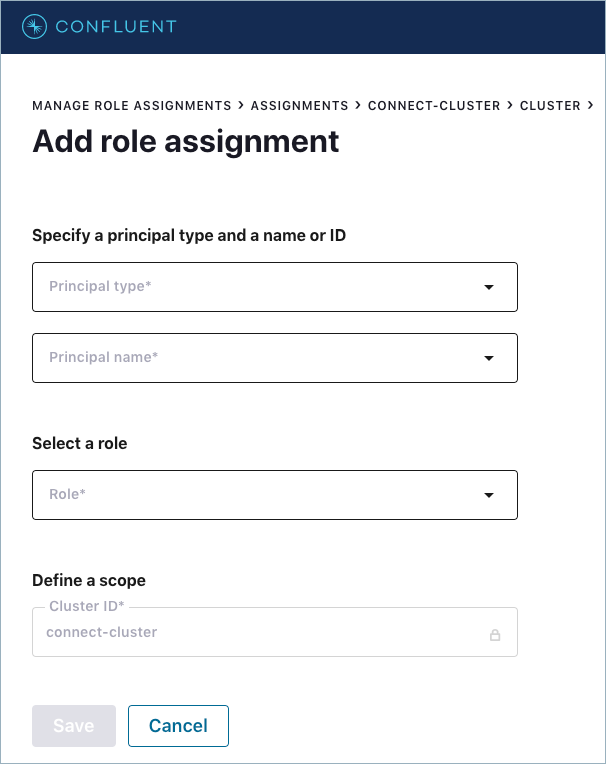
Add role assignment form¶
Complete this form to add a role assignment to a cluster or its resources. All fields are required. Some additional fields appear for the resource scope. In addition to assigning roles for a cluster, you can add a role assignment to the following cluster resources, depending on the cluster type:
Apache Kafka® cluster resources:
Consumer Groups
Topics
Transactional IDs
Tip
For more information about Transactional IDs, see this Confluent blog post and this stack overflow article.
Schema Registry cluster resources:
- Subjects
Connect cluster resources:
- Connectors
The following figure shows the Add role assignment form for a Connect cluster:
Fields¶
- Principal type
- LDAP/AD Group or User.
- Principal name
Principal name or ID. You can select an existing principal or create a new principal.
Important
The list of principals is pre-populated with those available from your LDAP/AD environment. If you create a principal rather than select an existing principal, ensure you create a corresponding principal in your LDAP/AD environment.
- Role
- List of available roles depending on the scope context (cluster or cluster resource).
- Define a scope
- Cluster ID or Resource ID
- View only.
- Pattern type
- Literal or Prefixed. Applicable to Resource scopes only (Consumer Group, Topics, Transactional ID, Subject, and Connector).
- Select or enter resource ID
Applicable to Resource scopes only (Consumer Group, Topics, Transactional ID, Subject, and Connector).
Important
If a user already has permissions granted to certain prefixes or literal patterns, the list is pre-populated with options for you to select. If you create a resource ID rather than select an existing one from the list, ensure you create a corresponding resource in Confluent Platform.
Add a role assignment (cluster scope)¶
Follow these steps to add a role assignment (role binding) at the cluster scope level.
Log in to Control Center.
From the Control Center Administration menu, click Manage role assignments.
Click the Assignments tab. The Assignments page appears.
In the Cluster ID column, click the underlined link for the cluster name that you want to add role assignments to. Any tabs appropriate for the cluster type appear, open to the Cluster tab by default.
Click + Add role assignment. The Add role assignment form appears.
Specify a Principal type of either Group or User.
Specify a Principal name or ID.
Tip
Type some characters to search for a principal.
Select a role from the Role list.
Click Save. The top banner displays the
Successfully created role assignmentmessage.
Add a role assignment (resource scope)¶
Follow these steps to add a role assignment (role binding) at the resource scope level.
Log in to Control Center.
From the Control Center Administration menu, click Manage role assignments.
Click the Assignments tab.
In the Cluster ID column, click the underlined link for the cluster name that you want to add role assignments to. Any tabs appropriate for the cluster type appear, open to the Cluster tab by default.
Navigate to the appropriate cluster resource tab:
- Consumer Group, Topic, or Transactional ID (Kafka clusters)
- Subject (Schema Registry clusters)
- Connector (Connect clusters)
Click + Add role assignment. The Add role assignment form appears.
Specify a Principal type of either Group or User.
Specify a Principal name or ID.
Tip
Type some characters to search for a principal.
Select a role from the Role list.
Complete the fields in the Define a scope pane:
Select the Pattern type of either Prefixed or Literal. For Prefixed, you do not need to enter an asterisk. It is prepended for you.
Type the Resource ID of the resource you are assigning a role to.
Tip
If you are assigning a role to a topic that does not exist yet, you can create a topic on the fly by clicking the Create new topic link.
Click Save. The top banner displays the
Successfully created role assignmentmessage.
Delete a role assignment¶
Delete a role assignment (role binding) using the Control Center UI. You can delete only one role assignment at a time. You must have an appropriate role to delete a role assignment. Deleting a role assignment removes access to a cluster or its resources for a user or group.
To use the CLI to delete a role assignment, see confluent iam rolebinding delete.
Delete a role assignment (cluster or resource)¶
Follow these steps to delete a role assignment (role binding) at the cluster or resource scope level.
Log in to Control Center.
From the Control Center Administration menu, click Manage role assignments.
Click the Assignments tab. The Assignments page appears.
In the Cluster ID column, click the underlined cluster link for the cluster name that you want to remove access from.
If applicable, navigate to the appropriate resource scope page for a cluster, such as:
- Consumer Group, Topic, or Transactional ID for a Kafka cluster.
- Subject for a Schema Registry cluster.
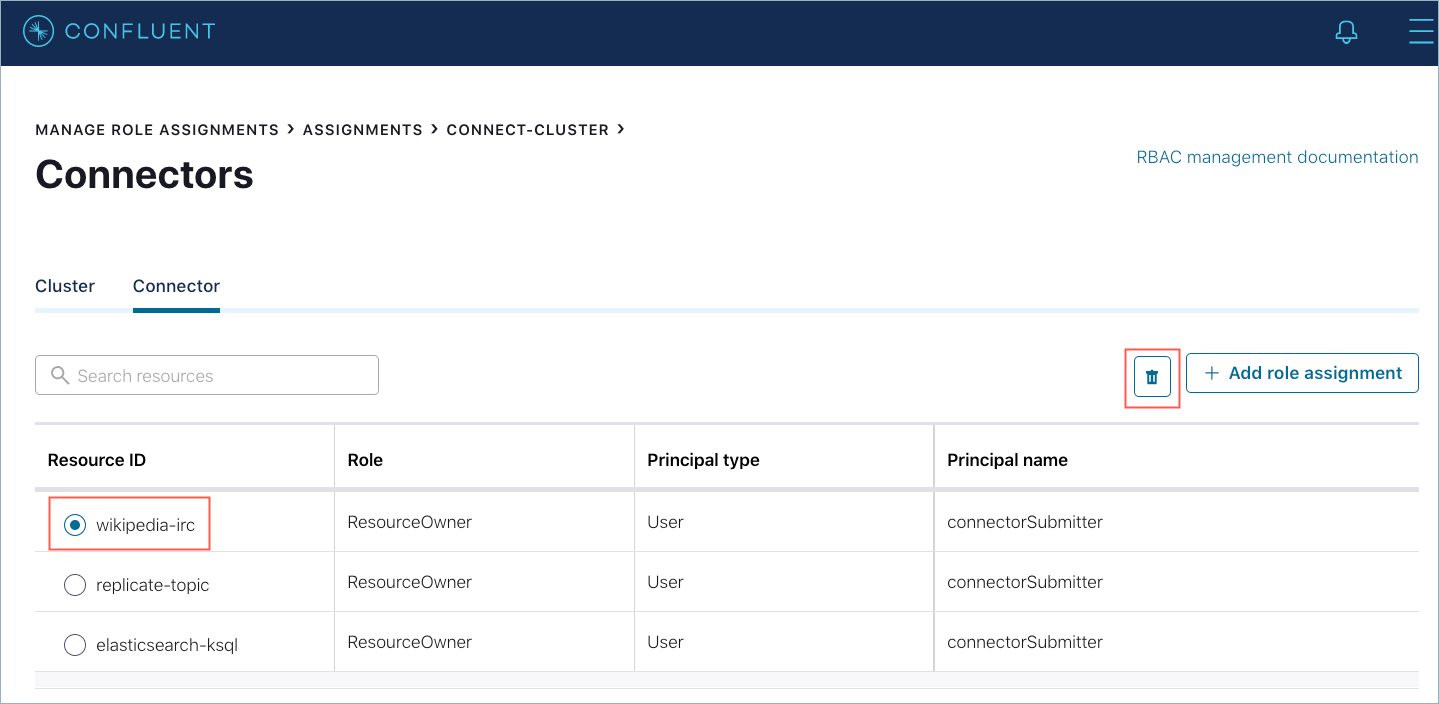
- Connector for a Connect cluster.
Depending on which scope:
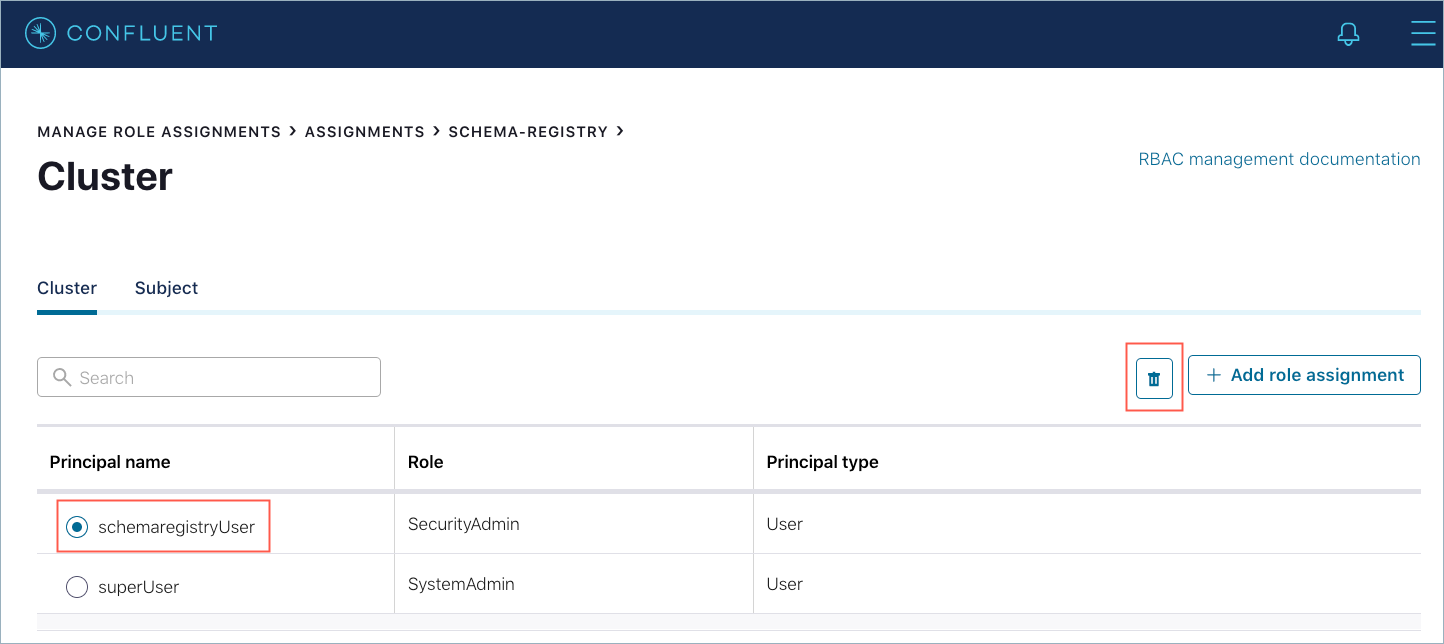
(Cluster) Select the role assignment to delete in the Principal name column.
(Resource) Select the role assignment to delete in the Resource ID column.
Click the trash icon. You are prompted to confirm deleting the role assignment.
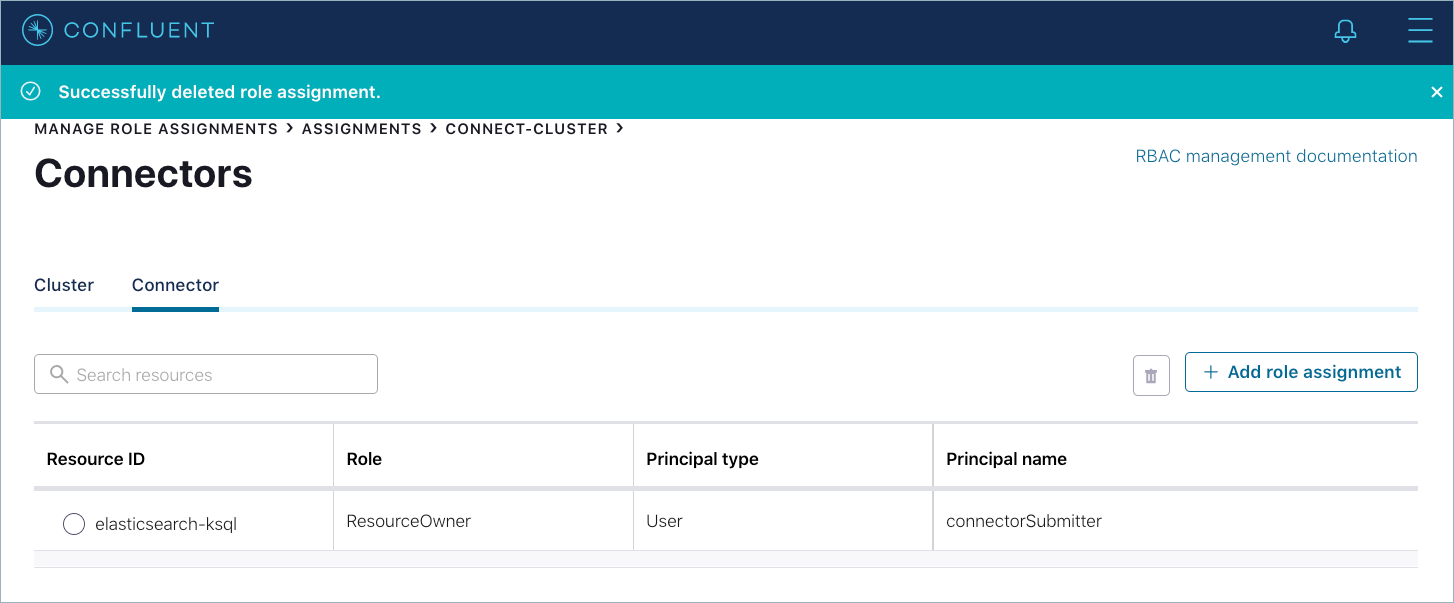
Type or copy and paste the Cluster or Resource ID into the text box and click Delete. The top banner displays
Successfully deleted role assignment.
Troubleshoot role assignments¶
Issue: User can add a role assignment successfully in Control Center but cannot view the newly added role assignment.
Reason and remedy: The user most likely is a broker super.user who also has a
ResourceOwner role. So that user has permissions to create a role assignment
but does not have permissions to view or manage the roles. The broker super.user
should be used to bootstrap the initial UserAdmin and SystemAdmin roles
and users, and not used thereafter.