Use Confluent Cloud Schema Registry to Connect to a Public Endpoint in a Private Networking Environment
If you have a private networking environment and you want to use Confluent Cloud Schema Registry, you must open outbound calls (egress) to a public Schema Registry endpoint. This is because Confluent Cloud Schema Registry is a multi-tenant Schema Registry.
Prerequisites
Confluent Cloud Schema Registry is enabled and configured. For more information about supported features, see Manage Schemas and Data Contracts in Confluent Cloud.
You must expose port
443or otherwise manage a TCP-HTTPS (SSL/TLS) port forwarding scheme. This is required to access the managed Confluent Cloud Schema Registry.
Configure Schema Registry to allow outbound calls to your private network
Navigate to a cluster to get to the Schema Registry settings in an environment.
On the information panel under Stream Governance API, you should see the Schema Registry endpoint. For example
https://confluent.us-east-2.aws.confluent.cloud.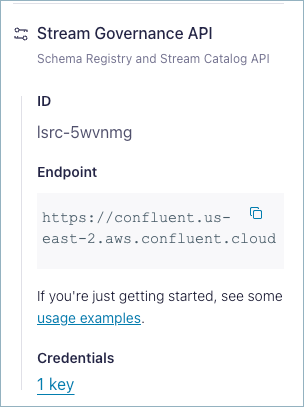
Open outbound calls to the Confluent Cloud Schema Registry endpoint. Follow the instructions based on your cloud provider.
- Azure VNet
Configure outbound call access for Azure networking components.
- AWS VPC
Configure outbound call access for these AWS VPC networking components:
Follow the instructions in the AWS Internet Gateway documentation.
Follow the instructions in the AWS NAT Gateway documentation.
Follow the instructions in the AWS NAT Instance documentation.
- Google Cloud VPC
Configure outbound call access for Google Cloud networking components.
Optional: Verify that your Schema Registry credentials are properly configured, where Schema Registry API key (
<schema-registry-api-key>), API secret (<schema-registry-api-secret>), and endpoint (<schema-registry-endpoint>) are specified.Run this command to authenticate with the cluster and list the topics registered in your schema.
curl -u <schema-registry-api-key>:<schema-registry-api-secret> \ <schema-registry-endpoint>/subjects
If no subjects are created, your output will be empty (
[]). If you have subjects, your output should resemble:["test2-value"]
Here is an example command:
curl -u <schema-registry-api-key>:<schema-registry-api-secret> \ https://psrc-lq2dm.us-east-2.aws.confluent.cloud/subjects