Connect to External Systems in Confluent Cloud¶
Confluent Cloud offers pre-built, fully-managed, Apache Kafka® Connectors that make it easy to instantly connect to popular data sources and sinks. With a simple UI-based configuration and elastic scaling with no infrastructure to manage, Confluent Cloud Connectors make moving data in and out of Kafka an effortless task, giving you more time to focus on app development.
- Source connector
- A source connector, such as the Microsoft SQL Server Source connector, ingests entire databases and streams table updates to Kafka topics. It can also collect metrics from all of your application servers and store these in Kafka topics, making the data available for stream processing with low latency.
- Sink connector
- A sink connector delivers data from Kafka topics into secondary indexes, such as Google BigQuery or batch systems like Amazon S3, for offline analysis.
- For connector billing information, see Kafka Connect Billing.
- For connector limitations, see Limits for Fully-Managed Connectors for Confluent Cloud.
Tip
- If you want to bring your custom connector to Confluent Cloud, see Install Custom Connectors for Confluent Cloud.
- Connect with Confluent is a program where partners work with Confluent to set up a Partner Integration. From this integration, your customers can start producing and consuming with a few clicks in your UI. For more information, see Connect with Confluent for Confluent Cloud.
Supported connectors¶
The following fully-managed connectors are supported by Confluent:
- ActiveMQ Source
- AlloyDB Sink
- Amazon CloudWatch Logs Source
- Amazon CloudWatch Metrics Sink
- Amazon DynamoDB Sink
- Amazon DynamoDB CDC Source
- Amazon Kinesis Source
- Amazon Redshift Sink
- Amazon S3 Sink
- Amazon S3 Source
- Amazon SQS Source
- AWS Lambda Sink
- Azure Blob Storage Sink
- Azure Blob Storage Source
- Azure Cognitive Search Sink
- Azure Cosmos DB Sink
- Azure Cosmos DB Source
- Azure Data Lake Storage Gen2 Sink
- Azure Event Hubs Source
- Azure Functions Sink
- Azure Log Analytics Sink
- Azure Service Bus Source
- Azure Synapse Analytics Sink
- Databricks Delta Lake Sink
- Datadog Metrics Sink
- Datagen Source (development and testing)
- Elasticsearch Service Sink
- GitHub Source
- Google BigQuery Sink (Legacy)
- Google BigQuery Sink V2
- Google Cloud BigTable Sink
- Google Cloud Functions Gen 2 Sink
- Google Cloud Functions Sink
- Google Cloud Pub/Sub Source
- Google Cloud Spanner Sink
- Google Cloud Storage Sink
- Google Cloud Storage Source
- HTTP Sink
- HTTP Source
- IBM MQ Source
- InfluxDB 2 Sink
- InfluxDB 2 Source
- Jira Source
- Microsoft SQL Server CDC Source (Debezium) [Legacy]
- Microsoft SQL Server CDC Source V2 (Debezium)
- Microsoft SQL Server Sink (JDBC)
- Microsoft SQL Server Source (JDBC)
- MongoDB Atlas Sink
- MongoDB Atlas Source
- MQTT Sink
- MQTT Source
- MySQL CDC Source (Debezium) [Legacy]
- MySQL CDC Source V2 (Debezium)
- MySQL Sink (JDBC)
- MySQL Source (JDBC)
- New Relic Metrics Sink
- OpenSearch Sink
- Oracle CDC Source
- Oracle Database Sink
- Oracle Database Source
- PagerDuty Sink
- PostgreSQL CDC Source (Debezium) [Legacy]
- PostgreSQL CDC Source V2 (Debezium)
- PostgreSQL Sink (JDBC)
- PostgreSQL Source (JDBC)
- RabbitMQ Sink
- RabbitMQ Source Connector
- Redis Sink
- Salesforce Bulk API 2.0 Sink
- Salesforce Bulk API 2.0 Source
- Salesforce Bulk API Source
- Salesforce CDC Source
- Salesforce Platform Event Sink
- Salesforce Platform Event Source
- Salesforce PushTopic Source
- Salesforce SObject Sink
- ServiceNow Sink
- ServiceNow Source
- SFTP Sink
- SFTP Source
- Snowflake Sink
- Solace Sink
- Splunk Sink
- Zendesk Source
Preview connectors¶
Important
Preview features are not currently supported and are not recommended for production use. A preview feature is a Confluent Cloud component that is being introduced to gain early feedback. Preview connectors and features can be used for evaluation and non-production testing purposes or to provide feedback to Confluent. Comments, questions, and suggestions related to preview features are encouraged and can be submitted to ccloud-connect-preview@confluent.io.
Note that Preview connectors are billed in the same way as other managed connectors. For more information, see Managed connectors and custom connectors.
The following Confluent Cloud connectors are available for preview:
Custom connectors¶
For information about bringing your custom connector to Confluent Cloud, see Install Custom Connectors for Confluent Cloud.
Cloud platforms support¶
The following table shows the cloud platforms supported by each connector.
| Cloud Connector | AWS | Azure | Google Cloud |
|---|---|---|---|
| Amazon CloudWatch Logs Source | Yes | Yes | Yes |
| Amazon CloudWatch Metrics Sink | Yes | No | No |
| Amazon DynamoDB Sink | Yes | No | No |
| Amazon Kinesis Source | Yes | Yes | Yes |
| Amazon Redshift Sink | Yes | No | No |
| Amazon S3 Sink | Yes | No | No |
| Amazon S3 Source | Yes | Yes | Yes |
| Amazon SQS Source | Yes | Yes | Yes |
| AWS Lambda Sink | Yes | No | No |
| Azure Blob Storage Sink | No | Yes | No |
| Azure Blob Storage Source | Yes | Yes | Yes |
| Azure Cognitive Search Sink | No | Yes | No |
| Azure Cosmos DB Sink | No | Yes | No |
| Azure Cosmos DB Source | No | Yes | No |
| Azure Data Lake Storage Gen2 Sink | No | Yes | No |
| Azure Event Hubs Source | Yes | Yes | Yes |
| Azure Functions Sink | No | Yes | No |
| Azure Service Bus Source | Yes | Yes | Yes |
| Azure Synapse Analytics Sink | No | Yes | No |
| Databricks Delta Lake Sink | Yes | No | No |
| Datadog Metrics Sink | Yes | Yes | Yes |
| Datagen Source | Yes | Yes | Yes |
| Elasticsearch Service Sink | Yes | Yes | Yes |
| GitHub Source | Yes | Yes | Yes |
| Google BigQuery Sink (Legacy) | No | No | Yes |
| Google BigQuery Sink V2 | No | No | Yes |
| Google Cloud BigTable Sink | No | No | Yes |
| Google Cloud Dataproc Sink | No | No | Yes |
| Google Cloud Functions Gen 2 Sink | Yes | Yes | Yes |
| Google Cloud Functions Sink | No | No | Yes |
| Google Cloud Pub/Sub Source | Yes | Yes | Yes |
| Google Cloud Spanner Sink | No | No | Yes |
| Google Cloud Storage Sink | No | No | Yes |
| Google Cloud Storage Source | Yes | Yes | Yes |
| HTTP Sink | Yes | Yes | Yes |
| HTTP Source | Yes | Yes | Yes |
| IBM MQ Source | Yes | Yes | Yes |
| InfluxDB 2 Sink | Yes | Yes | Yes |
| InfluxDB 2 Source | Yes | Yes | Yes |
| Jira Source | Yes | Yes | Yes |
| Microsoft SQL Server Sink | Yes | Yes | Yes |
| Microsoft SQL Server Source CDC (Debezium) [Legacy] | Yes | Yes | Yes |
| Microsoft SQL Server Source CDC V2 (Debezium) | Yes | Yes | Yes |
| Microsoft SQL Server Source | Yes | Yes | Yes |
| MongoDB Atlas Sink | Yes | Yes | Yes |
| MongoDB Atlas Source | Yes | Yes | Yes |
| MQTT Sink | Yes | Yes | Yes |
| MQTT Source | Yes | Yes | Yes |
| MySQL Sink | Yes | Yes | Yes |
| MySQL Source CDC (Debezium) [Legacy] | Yes | Yes | Yes |
| MySQL Source CDC V2 (Debezium) | Yes | Yes | Yes |
| MySQL Source | Yes | Yes | Yes |
| New Relic Metrics Sink | Yes | Yes | Yes |
| OpenSearch Sink | Yes | Yes | Yes |
| Oracle CDC Source | Yes | Yes | Yes |
| Oracle Database Sink | Yes | Yes | Yes |
| Oracle Database Source | Yes | Yes | Yes |
| PagerDuty Sink | Yes | Yes | Yes |
| Pinecone Sink | Yes | No | No |
| PostgreSQL CDC Source (Debezium) [Legacy] | Yes | Yes | Yes |
| PostgreSQL CDC Source V2 (Debezium) | Yes | Yes | Yes |
| PostgreSQL Sink | Yes | Yes | Yes |
| PostgreSQL Source | Yes | Yes | Yes |
| RabbitMQ Sink Connector | Yes | Yes | Yes |
| RabbitMQ Source | Yes | Yes | Yes |
| Redis Sink | Yes | Yes | Yes |
| Salesforce Bulk API 2.0 Sink | Yes | Yes | Yes |
| Salesforce Bulk API 2.0 Source | Yes | Yes | Yes |
| Salesforce Bulk API Source | Yes | Yes | Yes |
| Salesforce CDC Source | Yes | Yes | Yes |
| Salesforce Platform Event Sink | Yes | Yes | Yes |
| Salesforce Platform Event Source | Yes | Yes | Yes |
| Salesforce PushTopic Source | Yes | Yes | Yes |
| Salesforce SObject Sink | Yes | Yes | Yes |
| ServiceNow Sink | Yes | Yes | Yes |
| ServiceNow Source | Yes | Yes | Yes |
| SFTP Sink | Yes | Yes | Yes |
| SFTP Source | Yes | Yes | Yes |
| Snowflake Sink | Yes | Yes | Yes |
| Solace Sink | Yes | Yes | Yes |
| Splunk Sink | Yes | Yes | Yes |
| Zendesk Source | Yes | Yes | Yes |
Networking and DNS¶
For information about managed connector networking, see Manage Networking for Confluent Cloud Connectors.
Confluent Cloud API for fully-managed and custom connectors¶
For information and examples to use with the Confluent Cloud API for fully-managed and custom connectors, see the Confluent Cloud API for Managed and Custom Connectors documentation.
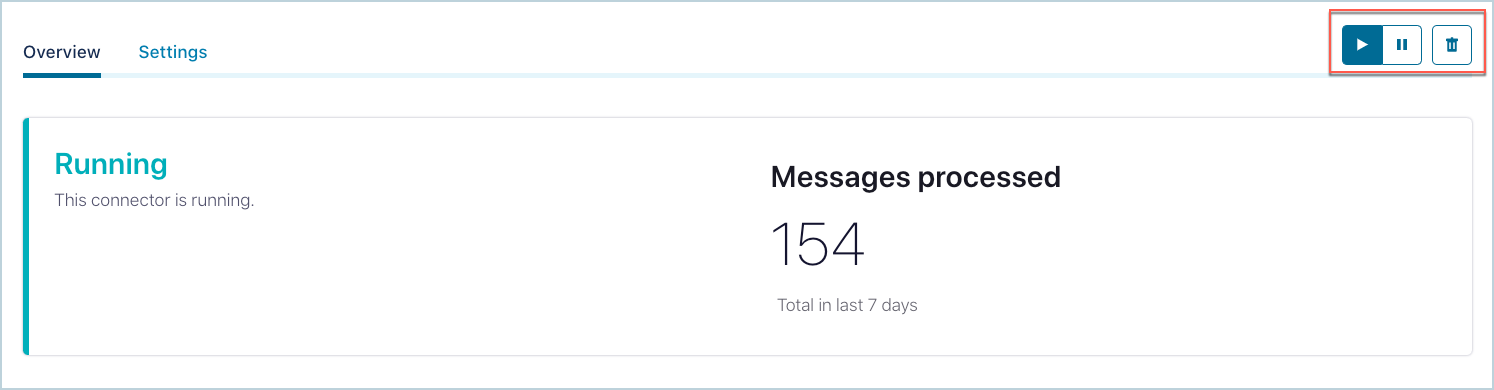
Cloud Console connector controls¶
You can use the GUI buttons to start, stop, pause, and delete a connector. Select and display one of your listed connectors to view the controls.
Connector data previews¶
For information about connector data previews, see Confluent Cloud Connector Data Previews.
Single message transforms¶
For information about using single message transforms (SMTs), see Configure Single Message Transforms for Kafka Connectors in Confluent Cloud.
View connector events¶
For information about viewing Confluent Cloud connector events, see View Confluent Cloud Connector Events.
Important
Viewing connector events is restricted to the OrganizationAdmin RBAC role. Viewing events is not available for other roles.
Service accounts¶
For information about setting up service accounts, see Confluent Cloud Connector Service Accounts.
RBAC for fully-managed connectors¶
For information about RBAC and fully-managed connectors, see RBAC for Managed and Custom Connectors in Confluent Cloud.
Dead letter queue¶
For information about accessing and using the Confluent Cloud Dead Letter Queue, see Confluent Cloud Dead Letter Queue.
Connector limitations¶
To view a list of connector limitations, see Limits for Fully-Managed Connectors for Confluent Cloud.
Manage Offsets¶
For information about managing offsets for managed connectors, see Manage Offsets for Fully-Managed Connectors in Confluent Cloud.